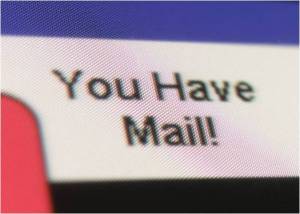
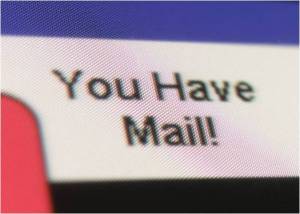
The email showed up in my Inbox one morning with the subject line: I have a genuine proposal of great benefit to you.
Yeah, that sounds totally genuine.
And thus I entered the exciting and dangerous world of scambaiting. Except it’s more tedious than exciting, and not too dangerous when the perpetrators sit on the other side of the planet and can’t afford air fare.
I hate scammers. I hate Rachael from Credit Card Services who calls twice a day (though sometimes she’s Bridget, and sometime Scott, and once in a while she’s Carmen) trying to get me to hand over my credit card numbers. I hate the emails that tell me I won a lottery I never entered in a country I’ve never been to. I am just waiting for some kid to call me pretending to be a grandson I don’t have, asking for bail money to get out of some totally bogus charge in Greece. And the fake Microsoft people are still trying to convince me that my computer is sending out error messages.
So I declared war.
Sorry to be the bearer of bad news, but the Do Not Call lists, state or federal, do nothing. I continue to report each and every call to them in the hopes of making any charges they do someday press just that tiny bit more massive. The email scammers are almost always outside our borders, sending false phone numbers to your caller ID, and no one has time to track them down. Therefore, all you can do to strike a glancing blow for Cosmic Justice is: Waste their time. Every minute they spend sending you an email or sitting on the phone writing down fictitious credit card numbers is a minute they can’t spend scamming some poor soul who might actually fall for it.

There are entire websites dedicated to people’s efforts to derail these scammers, and they are a font of good information and some great laughs. Following their advice I set up a new, free email account and instantly became Chloe, a pretty twenty-two year old, complete with a fetching photo from MS Office Clipart. (This wasn’t just wishful thinking—I thought her youth might explain her apparent naiveté in believing every story sent to her.) Chloe lives in a state I’ve never been to and works hard as a waitress at a Waffle House. I borrowed the phone number of Rachael from Credit Card Services, using the town it comes back to in a reverse lookup search—it doesn’t matter, since scammers won’t pay the long distance phone bill to actually call it. I invented a non-existent address on a real road with a real zip code.
Then I started writing back. I copied the body only of the emails that came to my legitimate email address and responded—they send out too many at a time to notice one coming back from an address they didn’t contact. I told Ms. Liza Wong from Malaysia that I would be happy to help distribute the dead philanthropist’s money to those less fortunate, and MegaMillions winner Jim McCullen that I would accept the responsibility of disbursing his winnings. I wrote back to a helpful FBI agent in New York (though his IP address said Madagascar) who had found a package of 4.1 million dollars with my name on it (literally) and just needed me to fill out some forms to complete delivery. I found this so helpful of him. Who says the federal government is suspicious and obstructive and overly concerned with things like income tax payments?
A co-worker of mine drew the short straw and thus has been trained in the art of downloading computers to find stashes of child porn and other crimes. She has become my go-to person with tentative questions about How This Stuff Actually Works. Unfortunately whenever I ask her something she tends to burst into Swahili, throwing around terms like ‘data dump’ and ‘NTFS access’. I asked her about the IP addresses for the three emails above (the scambaiters’ site taught me how to find those), since the first two said they were in other countries but their IPs came back to the US and Canada. She said they can route through other people’s IPs. I always believed McGee on NCIS tracing an email that bounces through IPs all over the world to be Hollywood hyperbole, but it turns out to be somewhat accurate. My co-worker can’t do it, perhaps because my city can’t afford the cool flat-screens, but it can certainly be done. But, she said, they would need the cooperation of the host IPs. Aha, I said. Unless they hacked them, she said. Oh, I sighed.
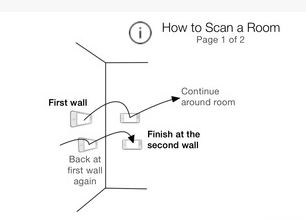
I GoogleEarthed (you know what I mean) my three IPs and found that the US one sat on the edge of a closed Air Force base (yikes) and the other two bordered high schools. My co-worker said they were probably using the free wi-fi—the same reason you see cars in the Starbucks parking lot when the place isn’t even open.

Nothing all that exciting has happened yet. The FBI agent never wrote back about my box of cash. The other two put me in touch with their banker, who sent me a very professional looking email detailing how, since I live in neither England or Malaysia, I have to deposit a sum to open a ‘temporal account’ to which my large windfall can then be deposited. The UK bank wants $1200, and the Malaysian one a more reasonable $640. I pleaded poverty (it would take my 22-year-old months to save that from her Waffle House paychecks!) and put them in touch with my banker at my fictional savings & loan. Chloe’s banker is an old family friend and looking out for the sweet girl’s interests, which is why he sent their bankers his own forms, which they must complete and return before they can be allowed to make a deposit at his fine institution. This will be difficult since the form demands to know things like your HBG number, which stands for “I Have No Idea, I Just Made It Up.” If they somehow work their way through this impossible task, then they may encounter further problems trying to fax it to another of Rachael from Card Services’ numbers.
Apparently both bankers found this daunting enough to give up on Miss Chloe, as neither she nor her bank manager have heard from them again. Jim McCullar gave up as well. Liza Wong hung in the longest with a forlorn, ‘have you heard from the bank, what’s going on?’ email.
I did have more success with today’s call from the persistent “Carmen” from “Credit Card Services.” They happened to call as I sat in front of my computer. Did you know you can Google “fake credit card number generator” and bring up a list of numbers for the major agencies? I kept a very polite representative on the phone for nearly fifteen minutes as she tried to ‘verify my balances’. I prepared to insist that, of course those are my correct credit card numbers, I’m looking right at them, but instead after a while she simply, quietly, failed to return from Hold.
But somewhere in the country, some other poor telephone owner got an extra ten minutes of peace this afternoon.
They’re welcome.
Close to the Bone hits forensic scientist Theresa MacLean where it hurts, bringing death and destruction to the one place where she should feel the most safe—the medical examiner’s office in Cleveland, Ohio, where she has worked for the past fifteen years of her life. Theresa returns in the wee hours after working a routine crime scene, only to find the body of one of her deskmen slowly cooling with the word “Confess” written in his blood. His partner is missing and presumed guilty, but Theresa isn’t so sure. The body count begins to rise but for once these victims aren’t strangers—they are Theresa’s friends and colleagues, and everyone in the building, herself included, has a place on the hit list.

Lisa Black spent the five happiest years of her life in a morgue. As a forensic scientist in the Cleveland coroner’s office she analyzed gunshot residue on hands and clothing, hairs, fibers, paint, glass, DNA, blood and many other forms of trace evidence, as well as crime scenes. Now she’s a certified latent print examiner and CSI for the Cape Coral Police Department in Florida. Her books have been translated into six languages and one reached the NYT mass market bestseller’s list.